AI-Powered Phishing Attacks Are Outsmarting Your Team—What Orange County Businesses Must Do Now
AI-Powered Phishing Attacks Are Outsmarting Your Team—What Orange County Businesses Must Do Now
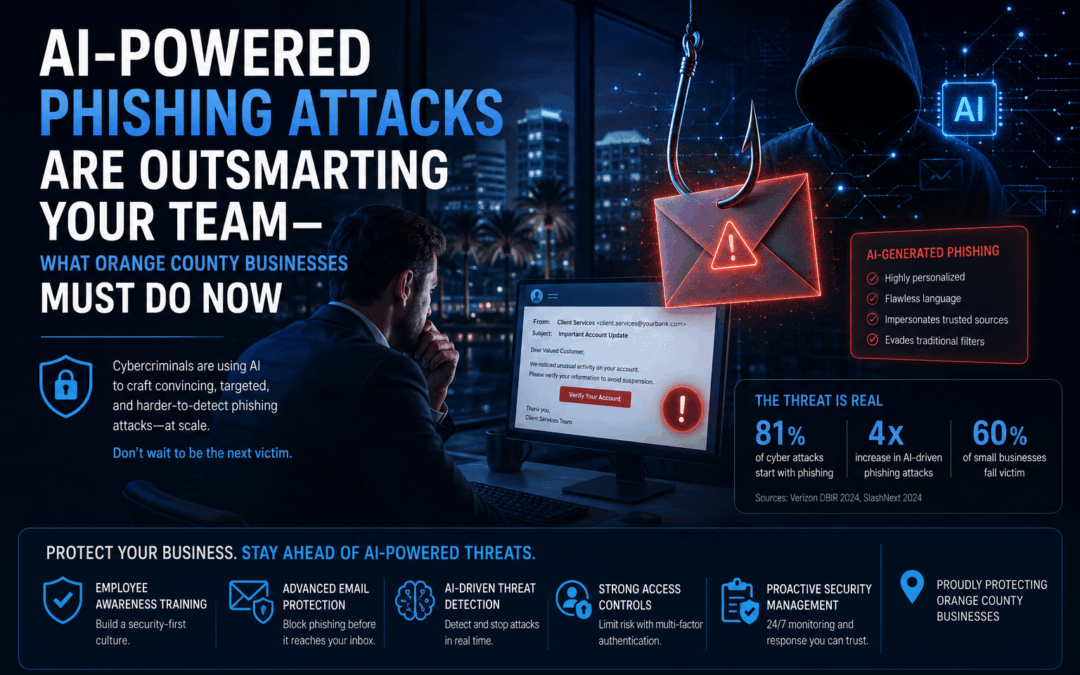
AI-generated phishing emails now achieve a 54% click-through rate. The threat your business faces in 2026 is fundamentally different from anything spam filters or annual security training were built to stop.
May 17, 2026 9 min read
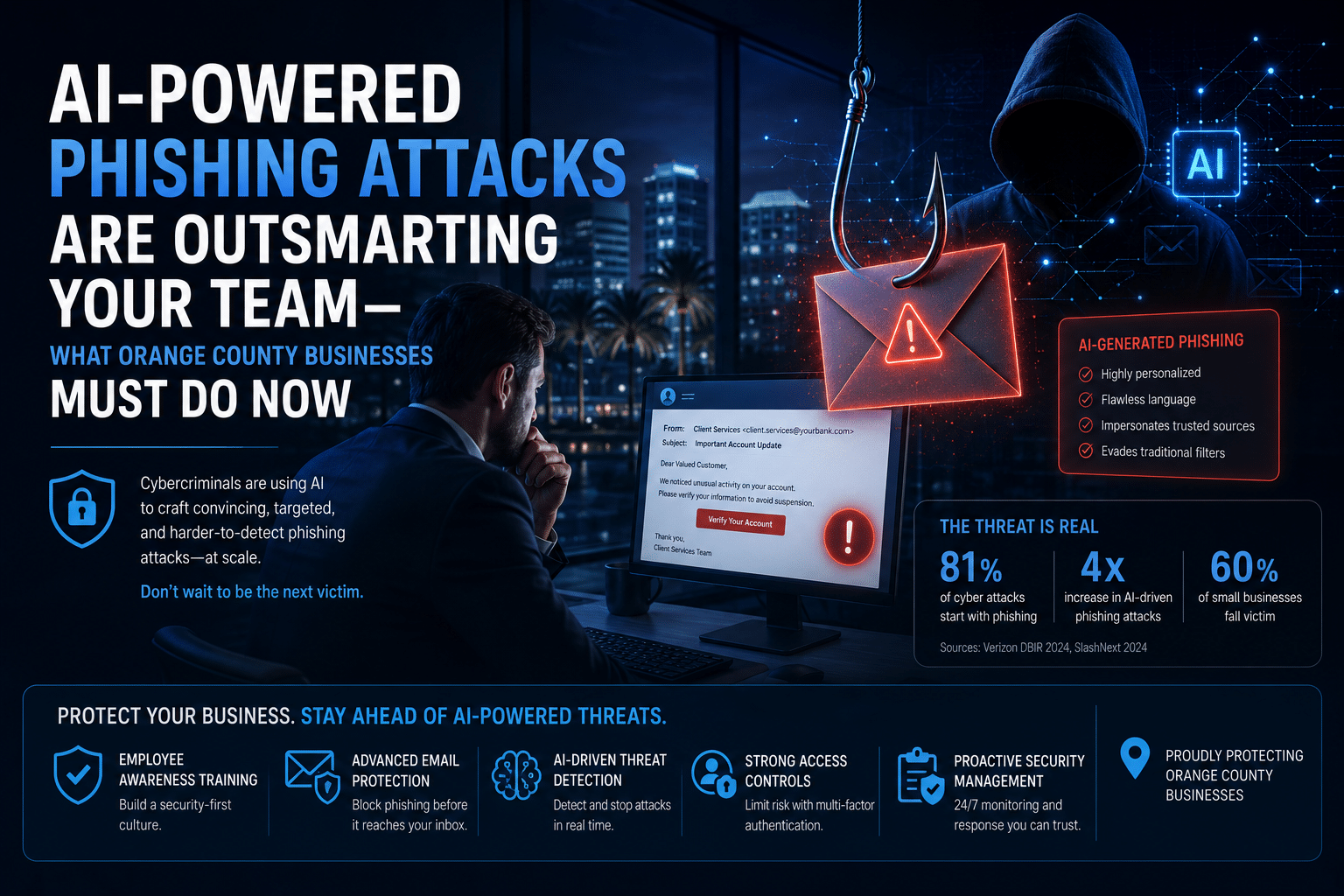
Your employees received 14 times more AI-generated phishing emails in December 2025 than they did just months earlier. By early 2026, more than half of all phishing emails arriving in corporate inboxes show evidence of AI authorship. These AI-powered phishing attacks are not an incremental upgrade to an old threat—they represent a fundamental shift in attacker capability, and most businesses in Orange County and across Southern California are not yet prepared for it.
Traditional phishing relied on volume over precision: send millions of clumsy emails with broken grammar and generic threats, hope a small percentage click. AI has inverted that model entirely. The success of AI-powered phishing attacks comes from large language models that craft individually tailored, grammatically perfect emails that reference real colleagues, recent business events, and plausible scenarios. The result is a click-through rate of 54%—compared to just 12% for human-written phishing. That means AI phishing converts at more than four times the rate of what your employees were trained to spot.
54%
click-through rate for
AI-generated phishing emails
4x
higher victimization rate
for SMBs vs. large enterprises
14x
surge in AI-generated
phishing since late 2025
How AI Has Transformed Phishing Overnight
AI has made nearly every one of those red flags obsolete. Modern attacks are generated by the same large language models that power widely used productivity tools. Attackers feed them publicly available information—LinkedIn profiles, company websites, press releases, social media posts—and instruct the model to write a believable email from a colleague, a vendor, or an executive. The output is indistinguishable from legitimate business correspondence. There are no spelling errors, no odd phrasing, no telltale signs. The email sounds exactly like someone your employee already trusts.
What makes this particularly dangerous for businesses across Orange County is the personalization at scale. An attacker no longer has to choose between a targeted, convincing email and a high-volume campaign. AI enables both simultaneously—thousands of individually tailored messages generated in minutes, each one reading as though it was written specifically for that recipient.
Five Types of AI-Powered Phishing Attacks Targeting Businesses Right Now
Understanding the specific forms these attacks take is the first step toward recognizing and stopping them. Here are the five most common AI-powered attack patterns observed against small and mid-sized businesses in 2026.
1. Spear Phishing with Executive Impersonation
AI generates hyper-personalized emails that appear to come from a company’s CEO or CFO, referencing real ongoing projects, recent company announcements, and authentic-sounding requests for wire transfers, credential resets, or vendor payment changes. Unlike older executive impersonation scams, these are tailored enough that even skeptical employees are frequently fooled.
2. Business Email Compromise (BEC) at Scale
Rather than needing to hack an email account, AI crafts messages that precisely match an executive’s writing style, typical vocabulary, and request patterns—learned from publicly available communications like press releases, interviews, or LinkedIn posts. The email looks like it came from the real person without the attacker ever needing account access.
3. Vendor and Supply Chain Lures
Attackers research a target company’s real vendor relationships and craft invoices, contract renewals, or payment update requests that precisely mimic the vendor’s branding and communication style. The April 2026 bank breaches both entered through a compromised shared vendor—the initial lure in each case was an AI-generated email targeting the vendor’s own employees first.
4. Deepfake Voice Phishing (Vishing)
AI voice-cloning technology creates convincing audio impersonations of executives or trusted colleagues, used in direct phone calls to pressure employees into approving urgent transactions or sharing access credentials. Financial firms across Orange County have reported Q1 2026 incidents involving calls that were indistinguishable from the real executive.
5. AI-Generated Fake Login Portals
Attackers build pixel-perfect replicas of Microsoft 365, Google Workspace, Salesforce, and other business platforms, served through convincing lookalike domains. Employees who click through end up on pages visually indistinguishable from the real login screen, surrendering credentials without any awareness that something is wrong.
Real-World Warning: April 2026
Two major U.S. banks were simultaneously compromised through a shared third-party vendor. In both cases, the entry point was an AI-generated phishing email targeting an employee at the vendor—not the banks themselves. One successful click at a smaller company became the breach vector for two major financial institutions. Your vendors’ security posture is your security posture.
Why Small and Mid-Sized Businesses Are the Primary Target
Only 11% of SMBs have adopted AI-powered defenses—meaning the same technology making attacks dramatically more effective is not yet protecting most businesses. The gap between attacker capability and defender capability has never been wider for companies in the 10-to-500 employee range. Attackers know this, and AI phishing tools are being actively optimized for SMB targets because the return per attack is high and the defenses are predictably weaker.
In Orange County and the Inland Empire, the businesses most exposed are professional services firms (legal, accounting, real estate, insurance), healthcare practices, defense contractors, and any organization that handles client financial data or sensitive personal information. These industries are prime targets because a single successful compromise yields either a large direct financial gain or highly marketable data. Managed cybersecurity services with continuous monitoring are the most effective structural response—but the first step is understanding the specific exposure your business faces today.
A Note on “AI-Resistant” Security Training
Many security awareness platforms now advertise AI-resistant phishing simulations, and these are genuinely valuable tools. But the research is clear and consistent: training alone reduces click rates by only 30–40% at best. The businesses that successfully defend against AI phishing combine training with layered technical controls—phishing-resistant MFA, email authentication protocols (DMARC/DKIM/SPF), and endpoint detection that identifies credential harvesting behavior even when the email itself looks completely legitimate. Training is a necessary layer, not a sufficient one.
Eight Steps to Reduce Your AI Phishing Risk Starting This Month
- Enable phishing-resistant MFA on all critical systems. Microsoft 365, Google Workspace, financial platforms, VPN—all of them. Standard SMS-based two-factor can still be bypassed through real-time phishing proxy attacks. App-based authenticators (Microsoft Authenticator, Google Authenticator) or hardware security keys provide significantly stronger protection for high-value accounts.
- Implement DMARC, DKIM, and SPF on your email domain. These protocols prevent attackers from spoofing your domain in emails targeting your own clients, vendors, and partners. They also cause many AI-generated impersonation attempts to fail authentication checks before reaching any inbox. If these are not configured, your domain can be weaponized against your clients without your knowledge.
- Run a current phishing simulation using AI-generated test emails. Most employees who passed security awareness training in 2023 or 2024 have not been tested against 2026-era AI phishing. Your existing click-rate benchmark is likely overly optimistic. Updated simulations provide an accurate picture of current vulnerability before an attacker does.
- Establish a verbal verification protocol for all financial transactions. Any email request to change banking details, authorize a wire transfer, or update vendor payment information must require a phone call to a known, verified number before action is taken. This single control stops the majority of BEC and vendor impersonation attacks regardless of how convincing the email is.
- Deploy endpoint detection and response (EDR) across all devices. Even if a phishing link is clicked, EDR software identifies credential harvesting behavior and malicious process execution at the endpoint before attackers establish a persistent foothold. Managed cybersecurity services in Orange County that include 24/7 EDR monitoring are particularly effective for businesses without a dedicated in-house security team.
- Audit your third-party vendor access and their security standards. The April 2026 bank breaches entered through shared vendor systems. Know which vendors have access to your network, what data they can reach, and what security posture they actually maintain. Consider requiring vendors with significant access to provide annual evidence of their security controls.
- Deploy advanced email filtering with AI behavioral analysis. Modern email security platforms use AI to identify AI-generated phishing patterns that traditional rules-based filters miss entirely. If your email filtering was configured more than 18 months ago, it likely predates the AI phishing surge. IT support providers in Orange County specializing in Microsoft 365 environments can typically deploy updated controls within a business day.
- Review your cyber insurance policy for AI-related coverage gaps. Many policies written before 2025 exclude AI-enabled social engineering attacks or carry sub-limits on business email compromise losses. Verify your current coverage reflects today’s threat landscape. Include a policy gap assessment as part of your annual compliance and risk management review.
The Bottom Line
The businesses that come through this wave unscathed will not be the ones that got lucky. They will be the ones that recognized the fundamental shift early enough to respond with layered technical controls, updated training, and a verified incident response process. For businesses in Orange County and Riverside, that response starts with an honest assessment of where you stand today—which controls you have, which gaps exist, and which threats your current setup is and is not designed to handle.
If you have not had a comprehensive cybersecurity review with a qualified partner in the last twelve months, the attack landscape has changed enough that your previous assessment is out of date. Defending against AI-powered phishing attacks requires working with experienced cybersecurity companies in Orange County who understand the current AI threat landscape is the fastest way to close that gap before attackers exploit it.
Is Your Business Prepared for AI-Powered Phishing?
TechHeights delivers managed IT services, cybersecurity, and compliance solutions trusted by 250+ businesses across Orange County and Riverside since 2007. Our security team can assess your current phishing defenses, identify gaps in your email authentication and MFA configuration, and implement the layered controls that stop today’s AI-generated attacks.


Recent Comments